Introduction
Currently, many applications or forms submitted by a citizen require the physical signature of the citizen. A digital signature takes the concept of traditional paper-based signing and turns it into an electronic “fingerprint.” This “fingerprint,” or coded message, is unique to both the document and the signer and binds them together. In essence, a digital signature has been done in the form of a handwritten signature. Some key features of the digital signature are non-acceptance, integrity, and authenticity.The Information Technology Act 2000 provides the required legal sanctity to digital signatures based on asymmetric cryptosystems.
The eSign Service
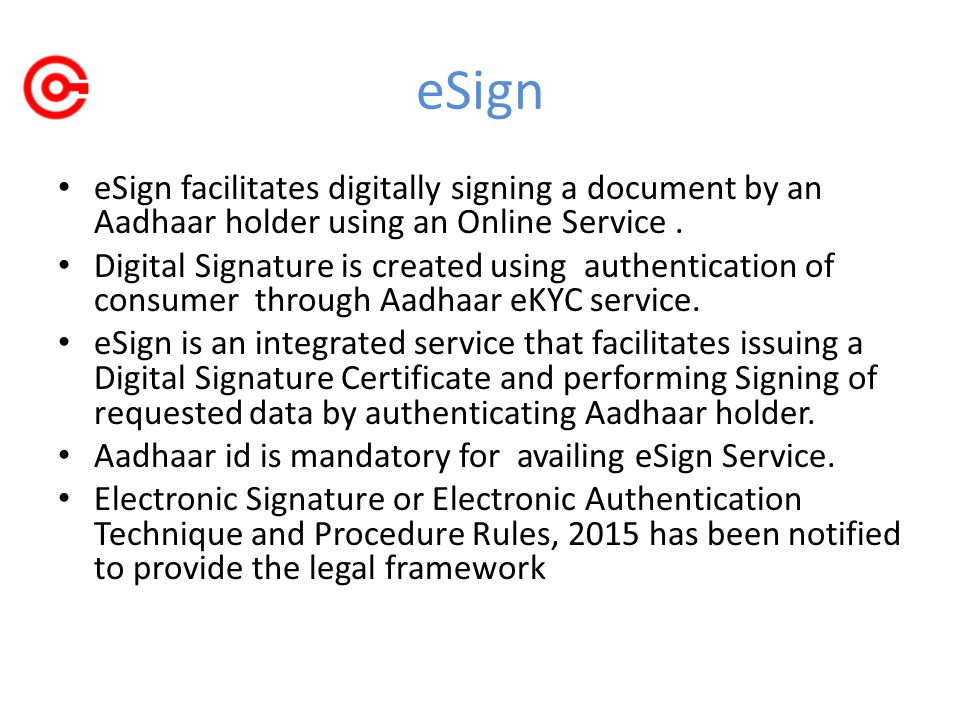
The Government of India declares a law in its Gazette Notification (REGD No. DL-33004/99 dated 28 January 2015), which provides the certification authority for providing e-sign service to citizens with Aadhaar ID.
The purpose of the E- sign service is to provide citizens with an online service to securely sign their documents in a legally acceptable form.
There are two major challenges involved: (A) user authentication and (b) reliable method of signing. Based on the first challenge, the basis based authentication is done and public key infrastructure (PKI) is used to safely sign the user document and establish the trust.
Citizens with Aadhaar IDs will be able to upload their documents to digitally sign their e-signing service. At the backend, validation of user is carried out using Aadhaar service and generates a key pair (a public key and a private key) for the user and signs the document. The user is provided with the digitally signed document and the Digital Signature Certificate.
C-DAC enables citizens to digitally sign their documents on-line, along with valid Aadhaar ID and registered mobile number through its e-Light initiatives.
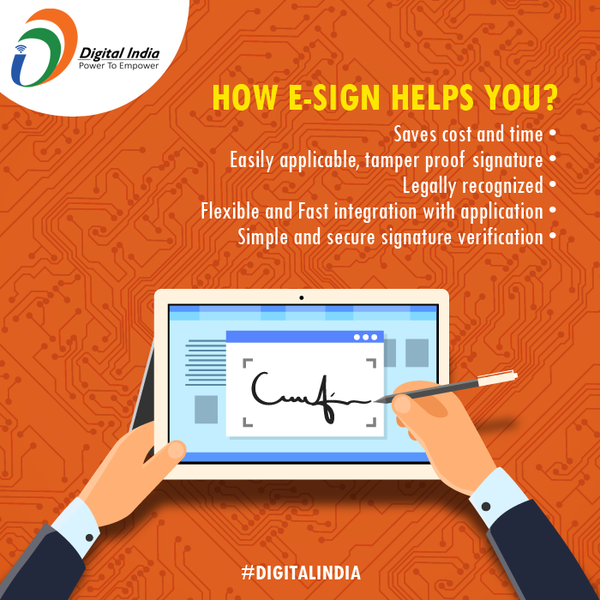
Salient Features
- Save cost and time
- Aadhaar-KYC based authentication
- improve user convenience
- Mandatory Aadhaar ID
- Easy to apply Digital Signature
- Biometric or OTP (optionally with PIN)based authentication\
- Verifiable Signatures and Signatory
- Flexible and fast integration with application
- Legally recognized
- Suitable for individual, business and Government
- Managed by Licensed CAs
- API Subscription Model
- Privacy concerns addressed
- Integrity with a complete audit trail
- Simple Signature verification
- Immediate destruction of keys after usage
- Short validity certificates
- No key storage and key protection concerns.

Benefits
Easy and secure way to digitally sign information anywhere, anytime
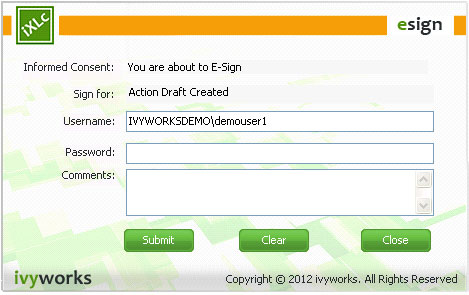
E-Sign is an online service without using a physical dongle that provides application services, provides functionality for certifying signatories and digital signatures of documents using the base e-KYC service.
Facilitates legally valid signatures
The E-sign process involves acceptance of digital signature certification in accordance with the provisions of Consumer Consent, Digital Signature Certificate Production, Digital Signature Producing and Information Technology Act. It implements compliance with the API specification and the API’s license model and a comprehensive digital audit trail has been established to verify the validity of the transaction, it is also protected.
Flexible and easy to implement
eSign provides configurable authentication choices in line with Aadhaar e-KYC service and conjointly record Aadhaar id to verify the identities of signers. Signature options include biometric or OTP authentication (optionally PIN) through a registered mobile in the base database ESign enables an easy way for millions of base holders to use legally valid digital signature service.
Respecting privacy
The eSign Service is governed by e-authentication guidelines. While the signatory’s authentication base E-KYC is used, the document is signed on a backend server.
Secure online service
which is the e-sign provider. eSign services are offered by trusted third party service provider, currently Certifying Authority. In order to increase security and prevent abuse, the certificate holders have been made on private key hardware security modules (HSM) and have been destroyed immediately after use.
Procedure
In this regard, the following procedure is provided for e-certification using the notification e-KYC services issued by the Government of India.
The authentication of an electronic record by e-authentication technology will be done by –
- A trusted third party service by customer key pair generation hardware security building storing the key pairs and digital signatures on modules provided trusted the third party will be proposed by the certifying authority (trusted third-party applications and certificates signed by the Client issuing a digital signature certificate to the certification authorization to Request for training),
- Issuance of digital signature certificate by the certification authority will be based on e-certification, details are given in the prescribed format, the information digitally verified from the base e-KYC services and the digital signature certificate electronic consent of the applicant,
- The methods and requirements for e-certification will be issued from time to time by the Controller,
- The security process for creating a customer’s key pair will be in accordance with the e-certification guidelines issued by the Controller,
- The standards mentioned in Rule 6 of the Information Technology (Certification Authority) Rule, 2000 will be followed, as long as they are related to the certification work of the public key of the applicant’s digital signature certificate, and
- The way in which a digital signature is authenticated, the information technology (certification authority) will comply with the standards specified in rule 6 of Rule 2000 so that they are related to the creation, storage, and transmission of digital signatures.
Who and where can use eSign
eSign have flexible subscription Model for individual users, business entities, and Governments. eSign based on OTP (optionally with PIN) level authentication is suitable where risks and consequences of data compromise are low but they are not considered to be of major significance. eSign based on Biometric (Fingerprint/Iris) level authentication ideal for and risks and consequences of data compromise are moderate. There may be a risk of substantial monetary value or fraud in the transaction, or access to personal information where the probability of malicious access is sufficient.
Credit- Vikas Pedi a, Wikipedia